[ad_1]
An updated version of the XLoader malware for Android devices does not require any user interaction to launch after installation, according to McAfee researchers (via BleepingComputer). Of course, downloading and installing malware requires clicking on a malicious link within an SMS message, but with this his XLoader variant, users no longer need to launch the malware manually.
Currently, malware is distributed through SMS texts on Android devices. If you are targeted, the SMS text contains a shortened URL that, when clicked, will take you to a website to download the mobile app’s Android APK installation file. McAfee states that “malicious activity is automatically initiated while the app is installed.”
This malware runs silently in the background and accesses all kinds of personal data on your Android device, including photos, messages, contacts, banking information, and more. Fortunately, this malware is very easy to spot, so if you have Google’s Play Protect services enabled on your Android device, you may already be protected. Here’s what to look for and how to check if Play Protect is active.
How to identify new XLoader malware
XLoader, also known as the MoqHao malware, was likely created by the financially motivated attacker Roaming Mantis, and McAfee said the malware’s code contains English, Korean, French, Japanese, German, and Hindi. We have identified some of the malicious pop-up messages written in , indicates the malware’s current target.
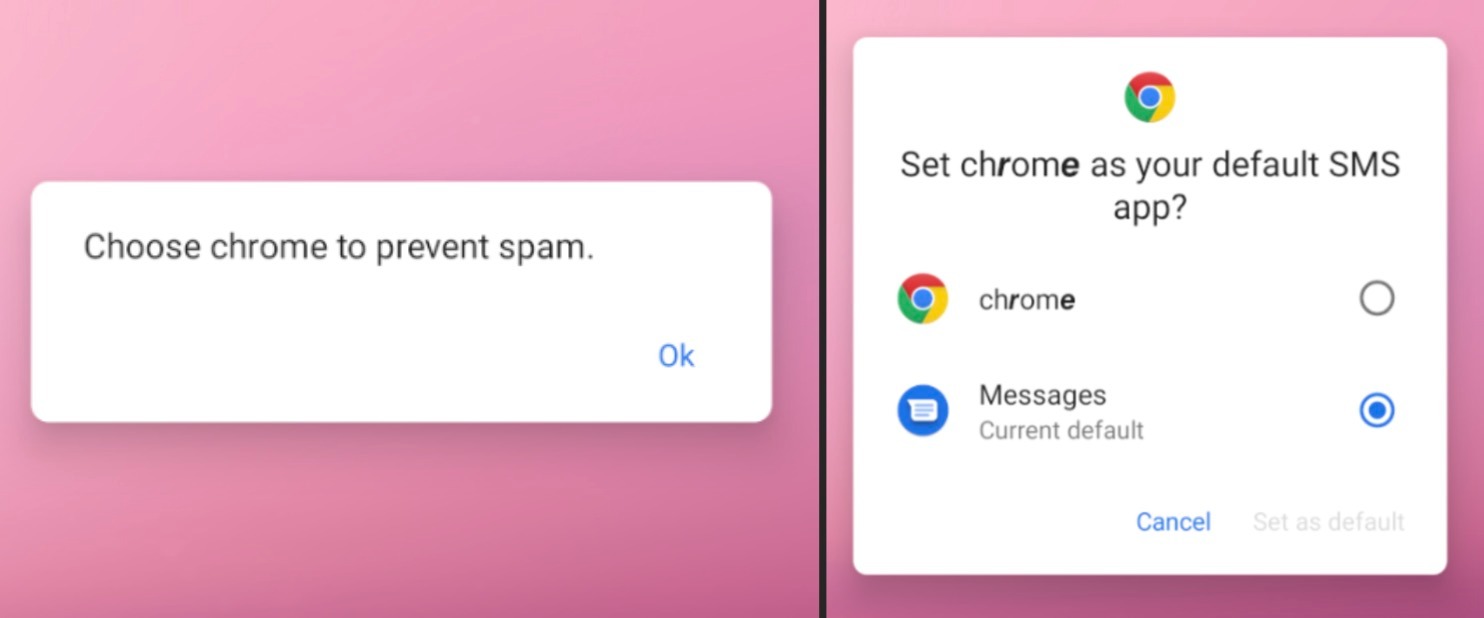
If you’re in an area that primarily speaks one of these languages, you may be at risk, but the warning signs that something is wrong are very obvious. In the malicious app’s first-launch permission request, which impersonates Google Chrome, you’ll notice that some characters are bold and others are not.
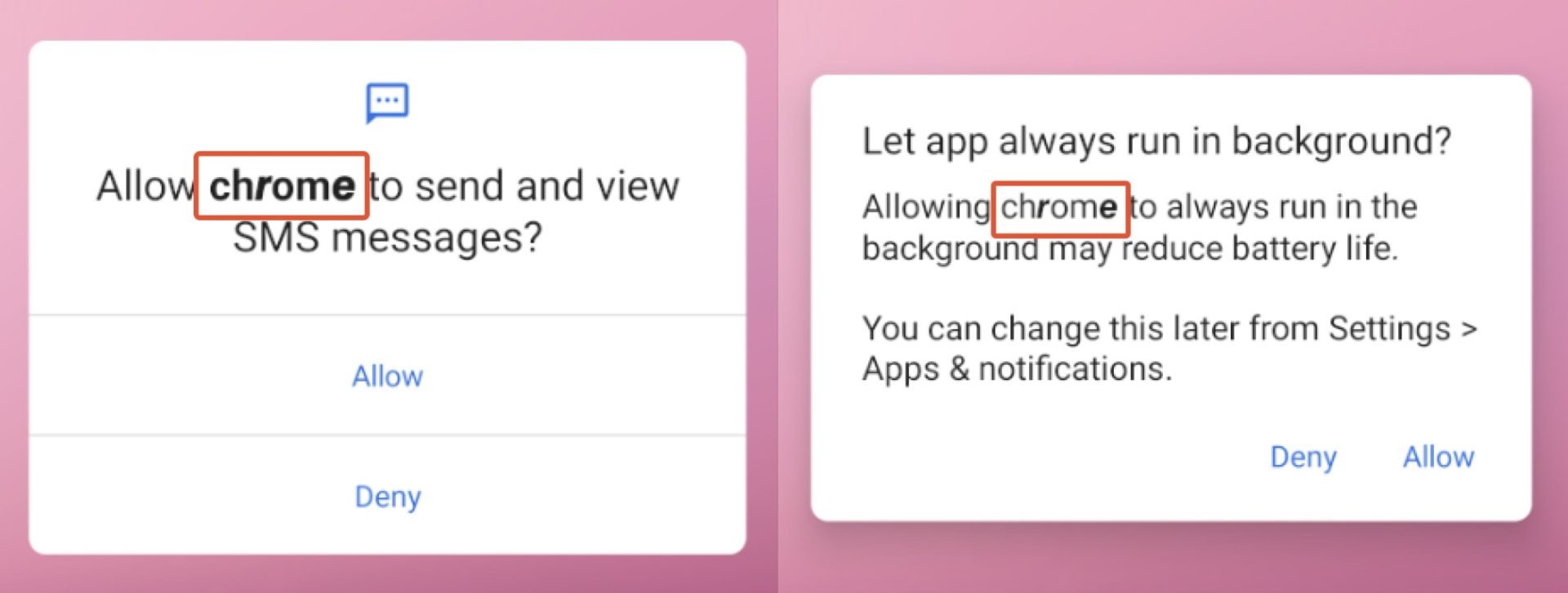
After these initial requests, the malicious app asks you to set “chrome” as your default SMS app, citing the reason “to prevent spam” to make you believe it’s the right decision. request. Again, random bold text will appear as a warning sign that something is wrong.
You should be wary of suspicious phishing URLs from Pinterest profiles. This is because this is the main way that XLoader malware currently targets victims and evades detection. McAfee outlines about 20 different commands that malware can currently execute. These five pose the biggest threats to personal data.
- Get photos: Sends all photos on the device to the hacker’s command and control (C2) server.
- getSmsKW: Send all SMS messages on your device to a C2 server. This may include sensitive information sent to family and friends.
- Send SMS: The XLoader malware allows you to send SMS messages from your device, potentially spreading phishing links to your friends and family.
- gcont: Export your contact list to a C2 server and provide hackers with direct contact information for targeted phishing attacks.
- Get phone status: Get device identification information such as IMEI, SIM number, Android ID, and serial number.
In a recent report, McAfee informed Google about the XLoader malware’s method of starting an app’s execution without manual activation by the user, and said that Google is “already working to implement mitigations to prevent this type of automatic execution. “There is,” he explains. Future Android versions. ”
McAfee further explained that “Android users are currently protected by Google Play Protect, which is turned on by default for Google Play services on Android devices.”
To check if Play Protect is active, Google Play AppTap profile icon Select in the top right corner settingTap about Click to open the drop-down menu. At the bottom, below Play Protect Certifiedthere should be a short message like this: Device is certified.
[ad_2]
Source link


